Cybersecurity & Compliance Services for Growing Businesses
Secure. Simplify.
Strengthen.


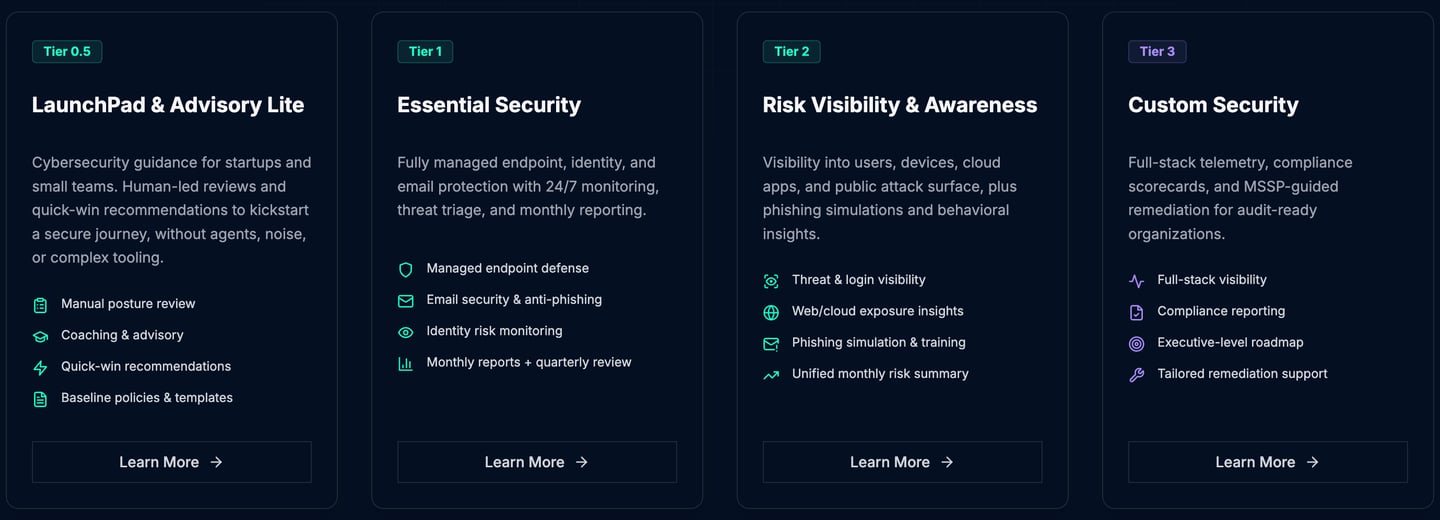
Service Bundles
Modular security services that scale with your business. Choose your stage of security maturity — Tiers are built to support your journey.
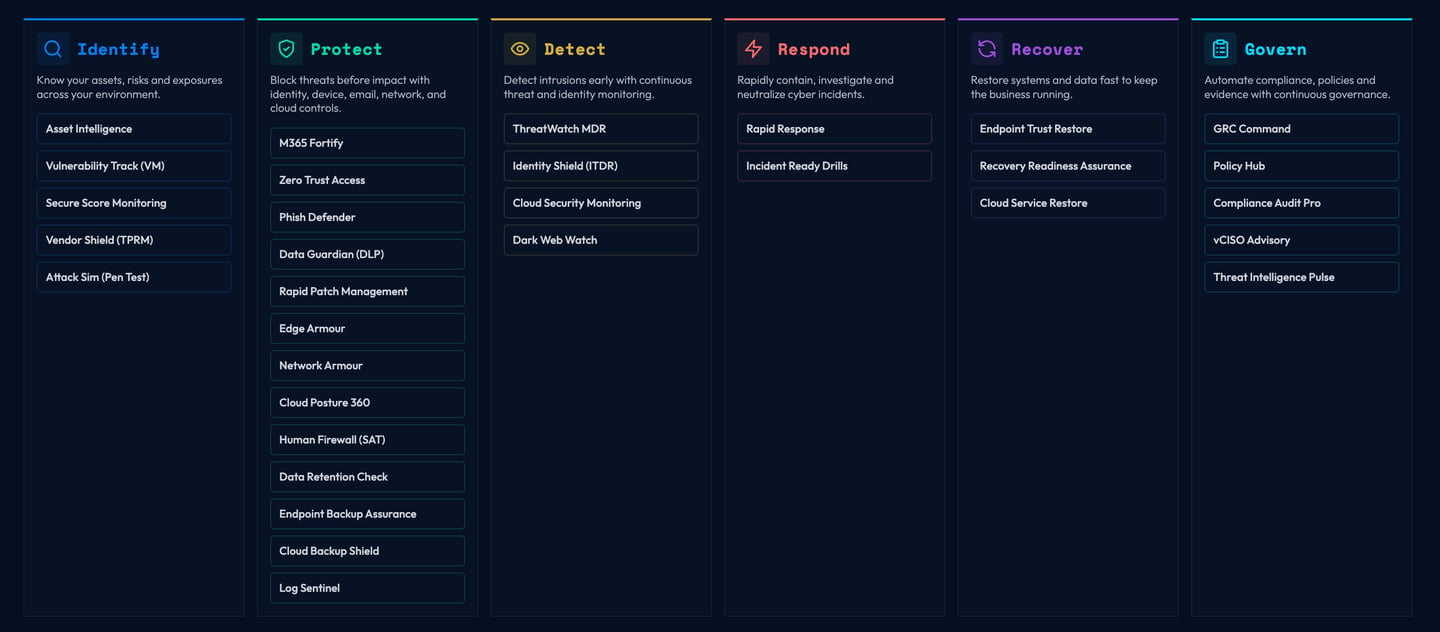
Service Atlas
Discover, Compare and Protect


We’re not a traditional MSP — we’re a Cyber MSSP engineered for the age of AI, automation, and relentless threats.




Built for Proof
Every control we deploy maps to verifiable evidence.
Driven by Clarity
We translate frameworks like NIST, CIS, and Essential Eight into business language.
Powered by People
Our analysts combine enterprise-grade skill with SMB affordability.
OUR ORIGIN STORY
Founded on a belief that cybersecurity should be measurable, scalable, and accountable — we built our MSSP from the ground up with a compliance-first mindset.
With governance leadership from Australia and security delivery from global engineers, we bring enterprise-grade resilience to SMB budgets..

Every service we deliver aligns with the six NIST CSF 2.0 functions —
MISSION
"Make enterprise-grade cyber resilience accessible, auditable, and affordable."
"Redefine Managed Security by merging governance, automation, and AI detection into a unified Cyber-as-a-Service model."
Ready to turn compliance into resilience?
VISION
Insights & Resources
Stay informed with the latest cybersecurity trends, compliance updates, and practical security tips.

Top 5 Cybersecurity Threats Facing SMBs in 2025
From ransomware to supply chain attacks, learn about the evolving threat landscape and how to protect your business.


Building a Security-First Culture: A Practical Guide
Security awareness training isn't enough. Here's how to embed security into your company's DNA from day one.


Honest Cyber’s quick response saved our network from a serious breach.
Reshma R.
Founder, ZenBubbles
★★★★★
Let's discuss your security needs
Fill out the form for a free assessment tailored to your security needs.
Bridging the gap between cybersecurity complexity and real business value. Enterprise-grade security for businesses of all sizes.
Reach out anytime for cyber help.
+91 9606606243
© 2025. All rights reserved.
info@honestcyber.com


+61 435105709


